Microsoft signed a driver being distributed in the gaming field, a malicious network filter rootkit. The driver is called “Netfilter,” a rootkit that redirects traffic to Chinese C2 IPs and aims to spoof gamers’ geo-locations to deceive the system and play from anywhere, said Microsoft.
Who first discovered the malicious driver?
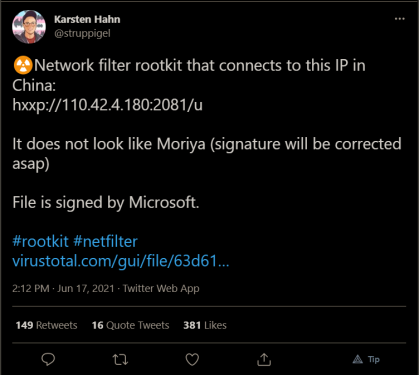
Karsten Hahn, a malware analyst at G Data, first noticed the malicious driver, posting it for the public on June 17 and simultaneously reaching out to Microsoft. Hahn reported that the code, a third-party driver for Windows that has been around the gaming community, connected to an IP address in China.
What is a Netfilter Rootkit malware?
- A rootkit is formed by two words: root and kit. The root stands for Windows Administrator, whilst the kit is basically a software program that can take over a personal computer without previously noticing the user.
- These Linux terms together merge into a rootkit, that once installed on the PC, can perform several actions such as resource hijacking, traffic scanning, or tracking every step of the user. Therefore, using rootkit malware, cyber attackers can perform keylogging or remote control of the computer leading to confidential data collection.
Microsoft response on the incident
The security response center team from Microsoft described the malware’s activity as “limited to the gaming sector specifically in China” and then explained its purpose:
“The actor’s goal is to use the driver to spoof their geo-location to cheat the system and play from anywhere. The malware enables them to gain an advantage in games and possibly exploit other players by compromising their accounts through common tools like keyloggers.”
The C2 (command-and-control) address – IP 110.42.4.180 – that the malicious Netfilter driver connected to belonged to Ningbo Zhuo Zhi Innovation Network Technology Co. Ltd., according to WHOIS records.

The company confirmed the incident on Friday, saying that it had started an internal investigation, has shared the signatures with security companies, and has added malware signatures to Windows Defender.
Suspended Third-Party Account
Microsoft stated in its announcement that it is now investigating a malicious actor who distributes malicious drivers in gaming environments. The attackers submitted drivers for certification through the Windows Hardware Compatibility Program (WHCP), which is designed to ensure that Windows-compatible software and hardware run smoothly on Windows 10, Windows 11, and Windows Server 2022 development, testing, and Distribute the driver.
And, obviously, you might do more harm to the already troubled gaming industry, which pandemic-bored attackers have hit. The impact included threats to all Sony PlayStation 3 IDs, triggering a ban on legitimate players on the network, hackers cracking pirated games by hijacking malware, and the Steam gaming platform used to host malware.
Eventually, the technology company has suspended the malicious-driver-distributing account and has reviewed the attacker’s submissions for additional signs of malware.
Microsoft said that the effects of this attack are limited. It hasn’t seen any sign of the WHCP signing certificate having been exposed, neither of any infrastructure having been compromised. Following its announcement, the rootkit-spreader is limiting its activity specifically to China and apparently isn’t targeting enterprises. Microsoft isn’t attributing the attack to a nation-state actor at this point.
According to the company, an important piece of the puzzle is the fact that the techniques used in the attack occurred after the utilization. Shortly put, a threat actor might “either have already gained administrative privileges to be able to run the installer to update the registry and install the malicious driver the next time the system boots or convince the user to do it on their behalf,” its announcement said.
Final thoughts
Digital certificates allow their owners to cryptographically link ownership to a public key for authentication purposes. They are one way for cyber attackers to escape detections they trick users into downloading malware, because it seems legitimate to their systems, as Tomislav Pericin from ReversingLab noted back in 2019. At that time, researchers spied cybercriminals duping certificate authorities by impersonating legitimate entities. They turned around and sold fraudulently purchased certificates on the black market, where they were purchased by other threat actors and used to digitally sign malicious files (mainly adware).
The company said it plans to share updates on how to improve its partner access strategy, verification, and signing processes to strengthen its protection. It says customers don’t have to take any action: just follow security best practices and deploy antivirus software, it recommends.
Attribution:
Photo by Mohammad Rezaie on Unsplash