Cyber Security Awareness Training with Automated Phishing Simulations
ATTACK Simulator can strengthen your security infrastructure by reducing the risk of data breach, helping your employees protect customer data, and complying with international standards of cyber security.
Security Awareness Training is critical
Given the current state of the world, there has never been a more opportune moment to engage in Security Awareness Training with ATTACK Simulator. Bad actors take advantage of the global pandemic, the shift in working environment and other opportunities to target unsuspecting individuals and companies.
Joe Biden: Ransomware threat becomes National Security Priority
As the ransomware threat against companies, institutions, and organizations in the U.S. is becoming increasingly present and likely imminent, Joe Biden plans on taking strategic action against it after elevating it to National Security Priority. Biden to set up...
LinkedIn breach with 92% of users’ data exposed
A second massive Linkedln breach exposes the personal data of 700 million LinkedIn users (nearly 92% of the total 756M users). Data has been sold on the dark web, with records including phone numbers, physical addresses, inferred salaries, and geolocation data. Based...
Cyberattack hits Spain’s Ministry of Labour and Social Economy on June 9
On June 9 this year, the Spanish Ministry of Labour and Social Economy (MITES) was hit by a cyberattack, only three months after a previous incident in March. Having an annual budget of nearly €39 million, this ministerial department is in charge of coordinating and...
ATTACK Simulator with its one of a kind phishing simulations aims at changing the bad stats and creating a cybersecurity oriented culture in every company.
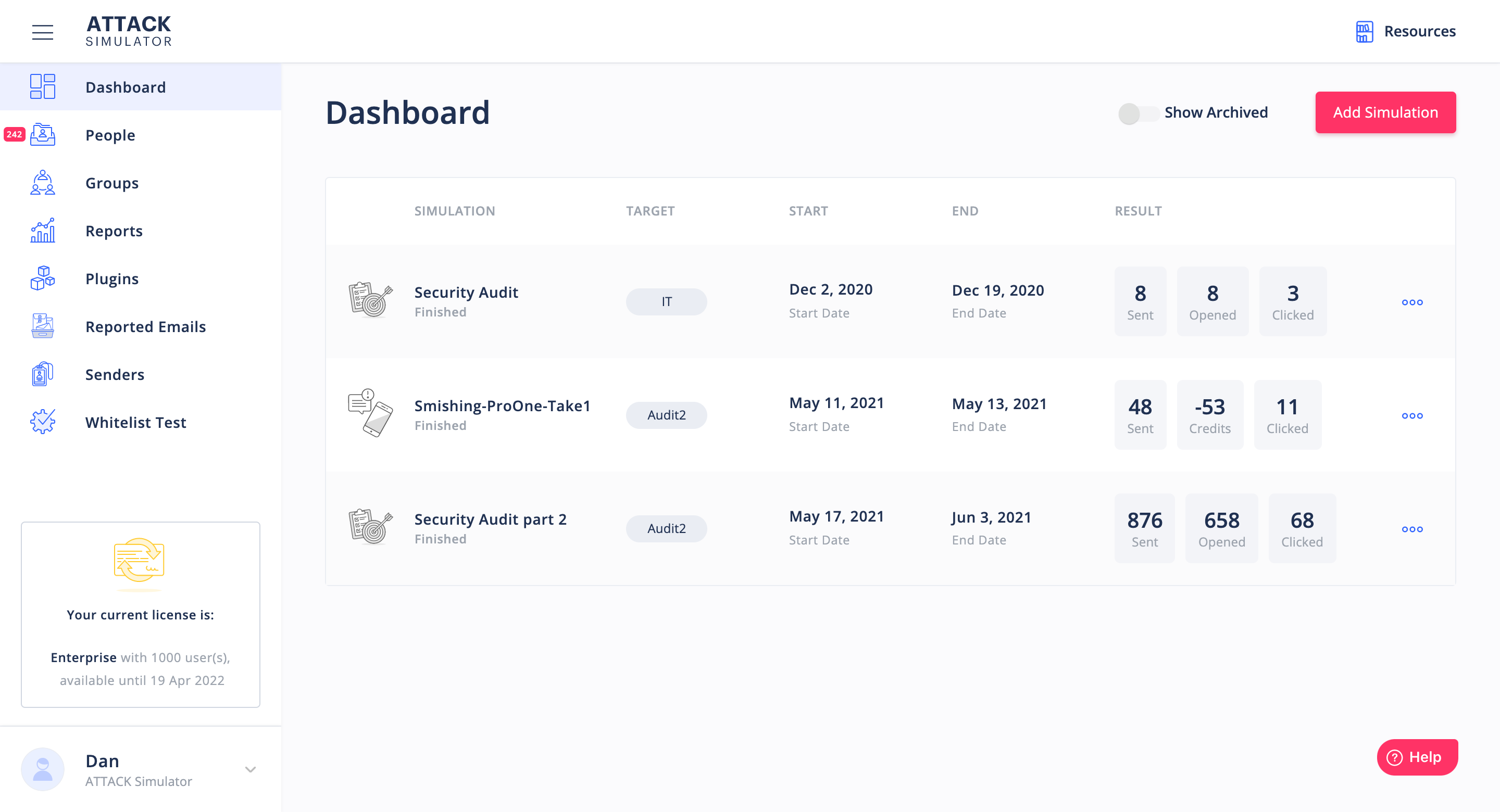
Over 1 300 companies enrolled
Over 53 000 employees trained
Over 245 000 simulations delivered
Over 50 000 successful attacks
ATTACK Simulator takes care of security so you can take care of business
Conducting business online involves security risks not worth taking. You can avoid falling victim to a cyberattack by taking adequate measures on time. ATTACK Simulator is here to make sure your employees are on top of security awareness with our automatic training plan, so you won’t have to worry about it anymore.
Who needs Security Awareness Training?
Cyber security skills are recommended to anyone who owns a computer. The perks of undergoing security awareness training include a better understanding of the digital world, how to avoid falling victim to a cyberattack, and how to best protect personal data.
Read more about specific industry cases to learn how security awareness concerns you.
Private enterprises
Private businesses and organizations are common targets of phishing attacks. As long as your enterprise processes customer data, in any form (personal data, financial data, health information, etc.), you are susceptible to costly cyberattacks that usually happen through your employees. Taking adequate measures to prevent the risks, and instilling appropriate information security management practices can spare you turmoil and secure your business. Security awareness training is the most effective way to educate your employees and empower your organization, providing great ROI.
Public enterprises
Individuals & Families
Individuals and families can suffer any type of cyberattack: from corrupt files that take control over their computer (malware), to credit card information loss (phishing attacks). Believing there is no reason you can be the target of a cyberattack can severely affect your security defense mechanisms which leads to losing valuable information and money. Besides making cyber language accessible, security awareness training provides you with skills demanded by the workforce, making you a desirable candidate for any position that involves working with data.