The aftermath of the ransomware attack carried out by the DarkSide group against Colonial Pipeline, the biggest fuel provider in the US, consisted of major disruptions throughout the US energy sector and served as a lesson in demonstrating the importance of protecting CNI (critical national infrastructure).
About Colonial Pipeline
Colonial Pipeline delivers fuels (gasoline, diesel, and jet fuel from Texas to New York), providing about 45% of the fuel consumed on the East Coast. It is the largest fuel pipeline in the U.S. The cyberattack happened after other similar high-profile attacks, such as the 2020 SolarWinds hack that targeted crucial government agencies – Defense, Treasury, State, and Homeland Security departments.
The ransomware attack had grave consequences
On May 7th of this year, the attackers compromised the company’s billing system, rendering it unable to bill its customers, which was why the pipeline operations had to be shut down. Colonial Pipeline reported the pipeline’s intentional halt took place because of the fear that the hackers could have exfiltrated data that would allow them to launch more attacks on the pipeline’s vulnerable parts.
The criminal group stole almost 100 gigabytes worth of data, threatening to publish it online unless the ransom was paid. The company paid almost 75 bitcoins within hours after the attack, equivalating to nearly $4.4 million. Unfortunately, the decryption tool the attackers offered in exchange for the ransom proved to be so slow that Colonial had to use its own backups to bring the compromised system back online.
Two days later, the fuel provider reported they would repair and restart a substantial part of the pipeline’s operations by the end of that week.
Due to the pipeline’s shutdown, the fuel shortages caused Charlotte Douglas International Airport to modify its flight schedules. At least two flights were reported to have had needed fuel stops or plane changes over the course of four days. In addition, the shortage affected in similar ways other airports, such as Hartsfield-Jackson Atlanta International Airport and at least five other airports serviced by the same pipeline.
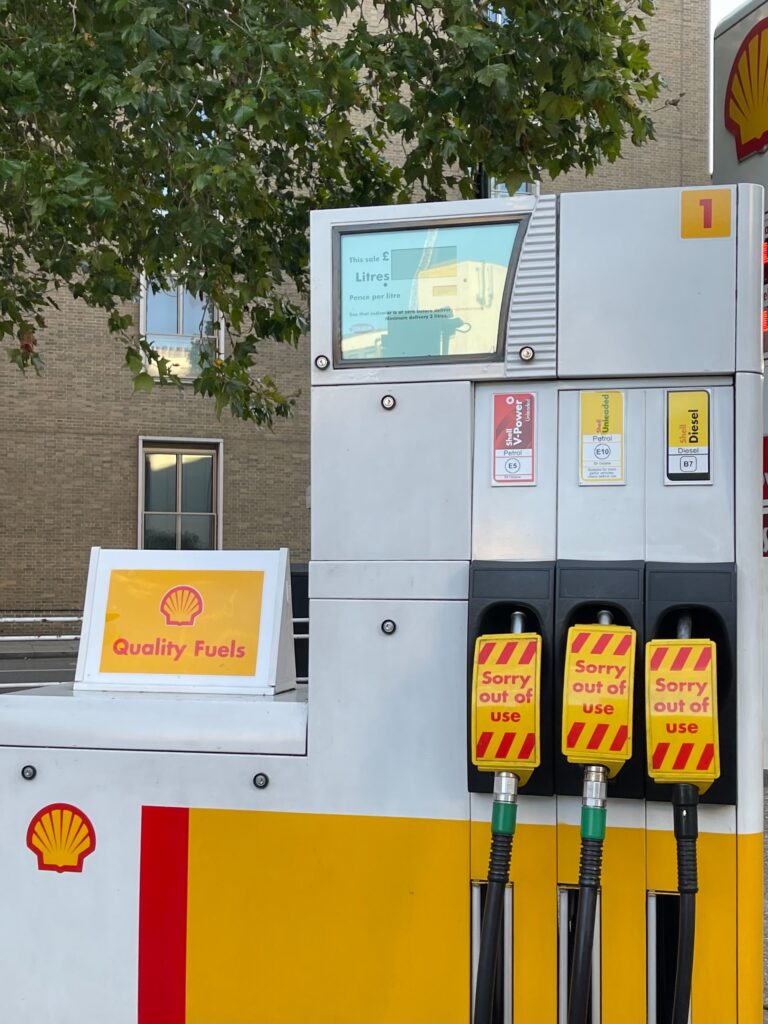
On the fourth day after the ransomware attack, while the pipeline was still shut down, panic buying had begun to cause shortages at filling stations. These shortages occurred in Alabama, Florida, North Carolina, Georgia, and South Carolina. 71% of filling stations in South Carolina and Southern Virginia were running short on fuel. Fuel prices leaped to over $3 a gallon, the highest they had been since 2014.
How the authorities responded
Joe Biden, the U.S. president, declared a state of emergency on May 9th in an attempt to alleviate shortages by removing restrictions concerning fuel transportation by road.
Georgia Governor Brian Kemp also declared a state of emergency on May 10th. This temporarily waived collection of the state’s taxes on diesel and gasoline. Pete Buttigieg, U.S. Transportation Secretary, and Jennifer Granholm, U.S. Energy Secretary, both warned against fuel hoarding.
The attack was linked to a group called DarkSide, first noticed in August 2020, located in Eastern Europe. They stated on May 9, avoiding directly mentioning the ransomware attack, that “our goal is to make money, and not creating problems for society.”
After a six-day halt, the pipeline’s operations were restarted at 5 p.m. on May 12th. However, Colonial Pipeline stated that various markets supplied by the company would continue experiencing intermittent service disruptions during the restart. The pipeline operations were fully restarted by May 15th.
Despite the authorities best efforts, 10,600 gas stations were still out of fuel as of May 18th.
The head of Colonial Pipeline, Joseph Blount, stated on June 8th that the hackers compromised their systems and caused such massive disruptions in their operations using one password.
“In the case of this particular legacy VPN, it only had single-factor authentication,” Blount said. “It was a complicated password, I want to be clear on that. It was not a Colonial123-type password.”
Ransom partially recovered after investigations
Further proof indicated that the DarkSide group was indeed located in Russia, although there was no evidence that the Russian Government was behind the ransomware attack, Biden said on May 10th.
The DarkSide group has launched ransomware attacks against 99 organizations, requesting an average payment of $1.9 million. They received 17% of the ransoms collected ($15.5 million), with the remaining 83% ($74.4 million) going to affiliates.
The Department of Justice announced on June 7 that they were able to recover a large part of the ransom payment (63.7 Bitcoins out of 75), but due to a drop in Bitcoin market value, they were worth only $2.3 million.
Ransomware attacks have become increasingly sophisticated and aggressive, especially in the context of the COVID-19 pandemic. As a result, stronger precautions need to be established, and Cybersecurity Awareness training is always a great idea for any company, be it small or big.
Sources:
ComputerWeekly https://www.computerweekly.com/news/252500508/Colonial-Pipeline-ransomware-attack-has-grave-consequences
ABC https://abcnews.go.com/Technology/ransomware-cyberattacks-rise/story?id=77832650
Attribution:
Feature Image: Photo by Jacob Morrison on Unsplash
Photo by John Cameron on Unsplash